In this blog, I will show you how to use Cisco ISE to authenticate users into APC Network-enabled devices such as PDU or UPS using Radius.
Radius Vendor-Specific Attributes (VSA)
There are various dictionaries created for different vendors and attributes can be added to each of these dictionaries. Each attribute, in general, defines the different roles of device administration a user could get when they log in to the network device. This eliminates the need to configure and define local accounts on the devices.
Step 1 - Import the APC dictionary
I'm going to import the APC vendor dictionary into ISE. I obtained the dictionary from the APC website which is referenced at the bottom of this blog. Save the following contents into a file called apc-dict.APC
VENDOR APC 318
BEGIN-VENDOR APC
ATTRIBUTE APC-Service-Type 1 integer APC
VALUE APC-Service-Type Admin 1
VALUE APC-Service-Type Device 2
VALUE APC-Service-Type ReadOnly 3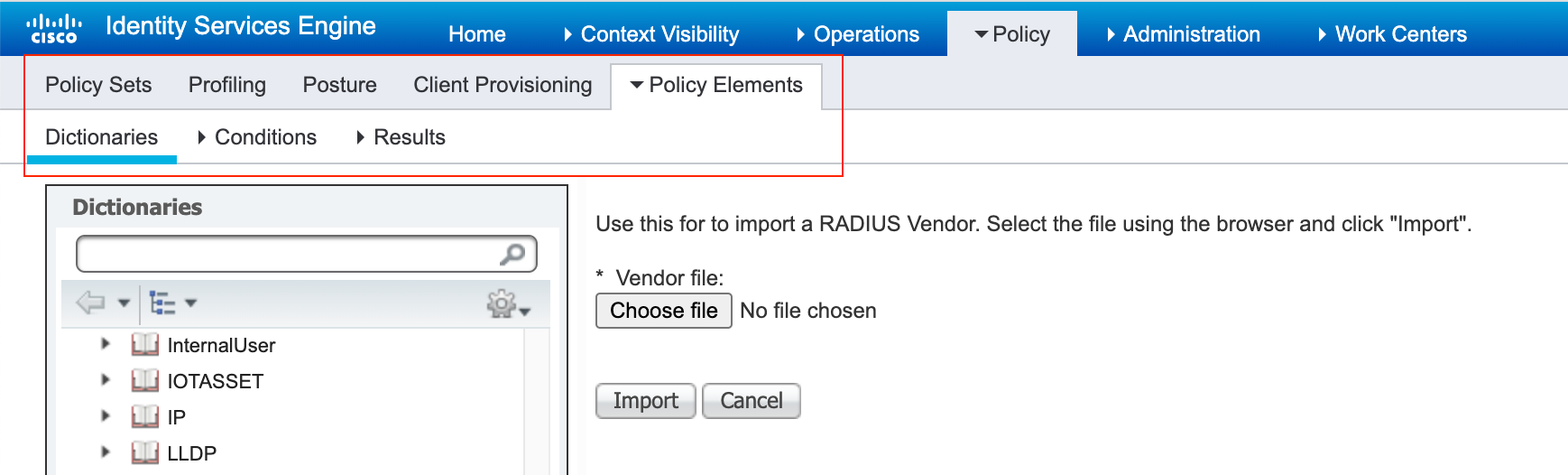
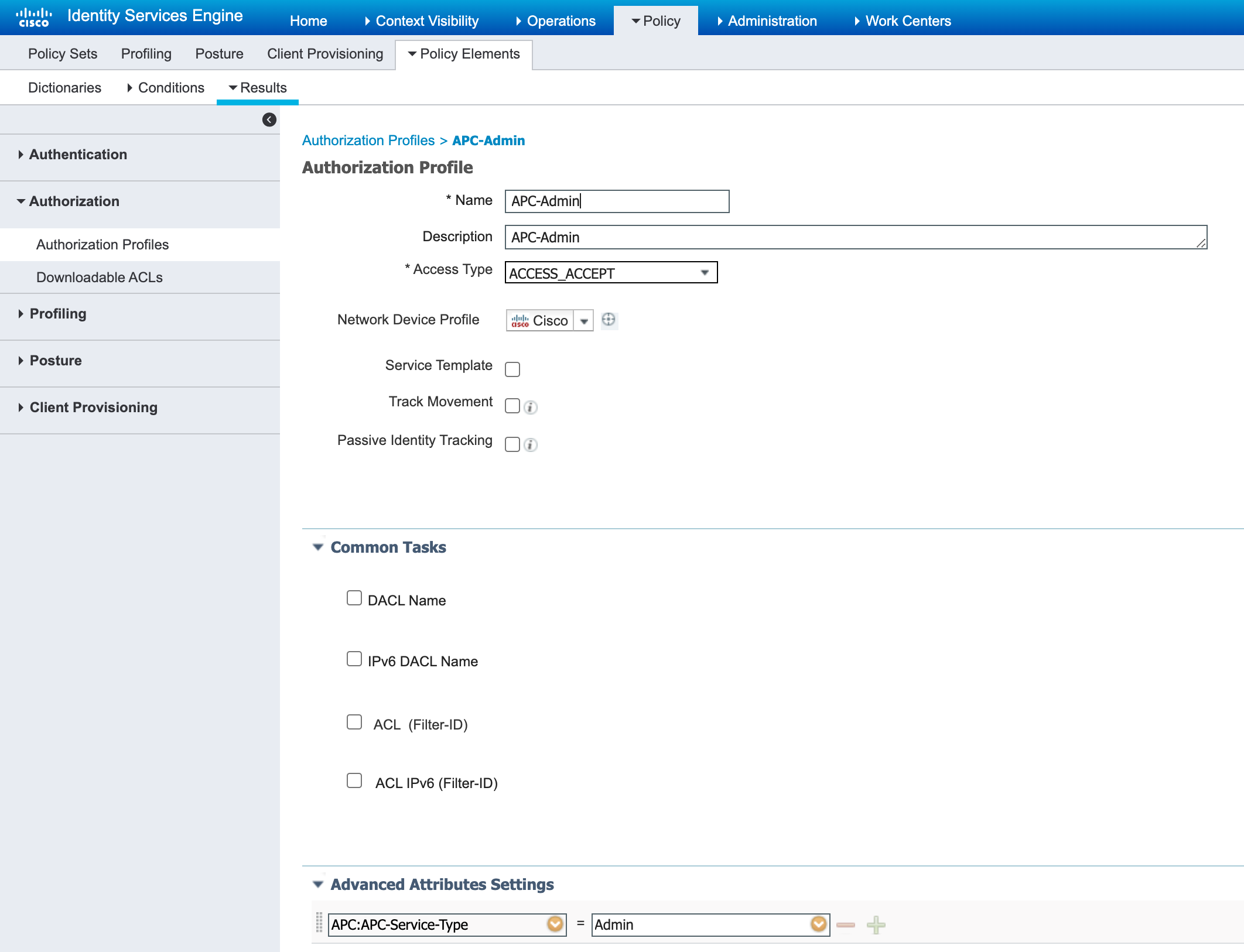
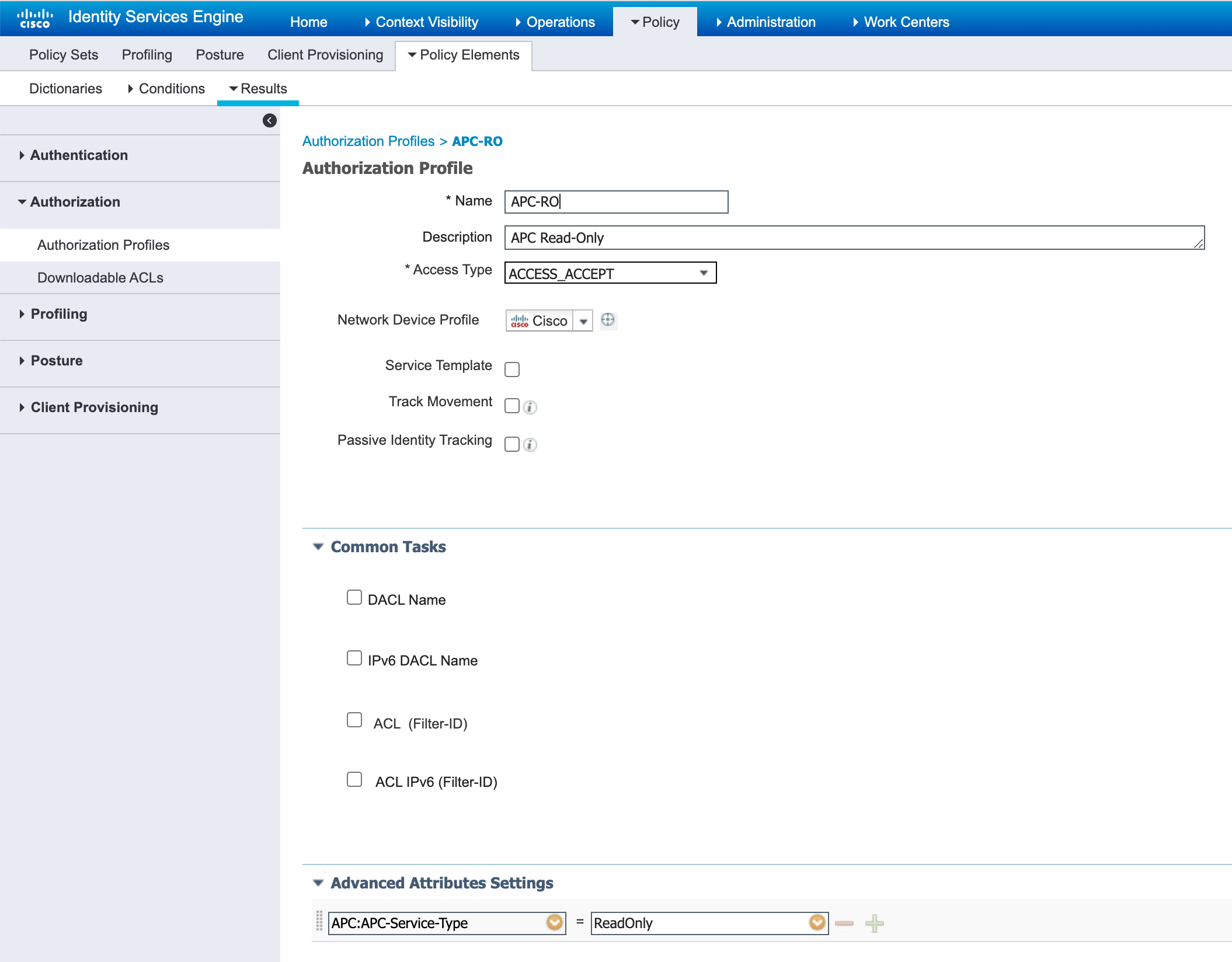
Step 2 - Configure authorization profiles
I'm going to create two authorization profiles - one with read-only access and another one with admin access.
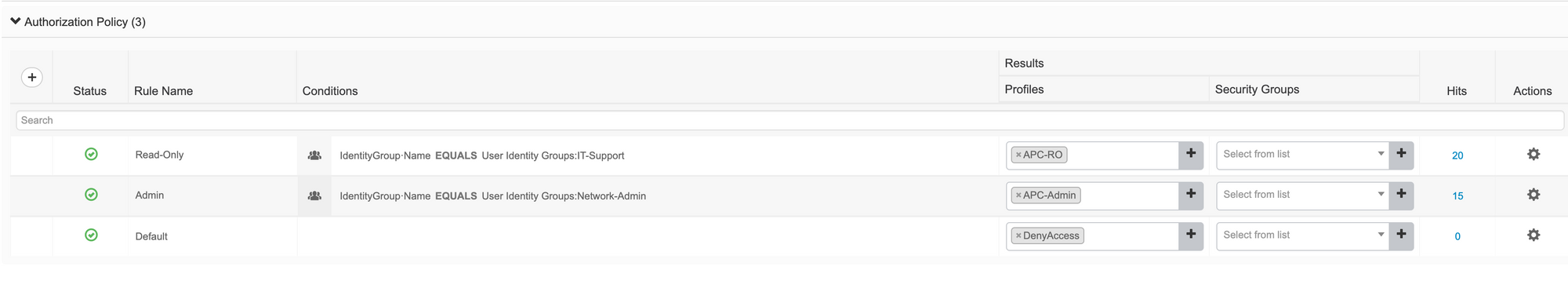
Step 3 - Configure authorization policies
Configure authorization policies and reference the profiles we just created. I've created a simple policy where the IT-support gets read-only access and Network-Admins get full admin access.
Reference


Thank you for reading. As always your comments and feedbacks are always welcome.